In the high-stakes world of federal cybersecurity, where one weak link can bring down an entire system, two powerhouses have locked in formation and gone full throttle. The Office of Management and Budget (OMB) and the General Services Administration (GSA) are rewriting the playbook on how the U.S. government tackles cloud security. Their mission? To streamline FedRAMP reporting, sharpen cloud security metrics, and give federal agencies the real-time intelligence they need to dominate in a rapidly evolving threat landscape.
FedRAMP Modernization Takes Flight
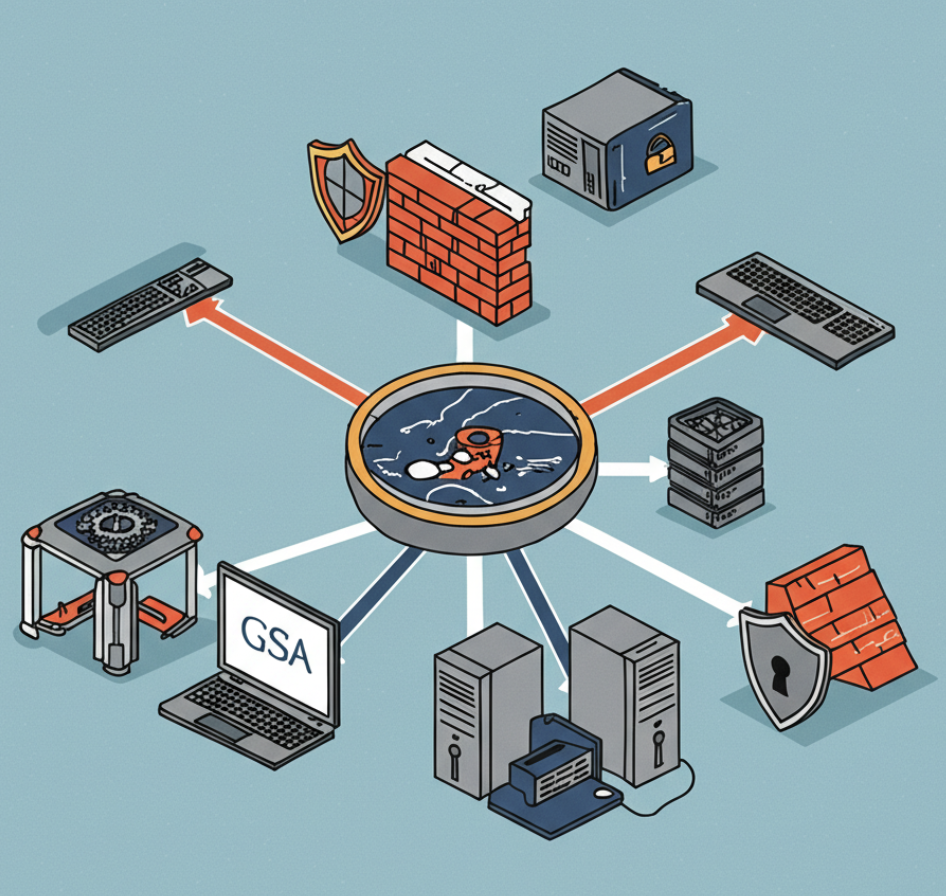
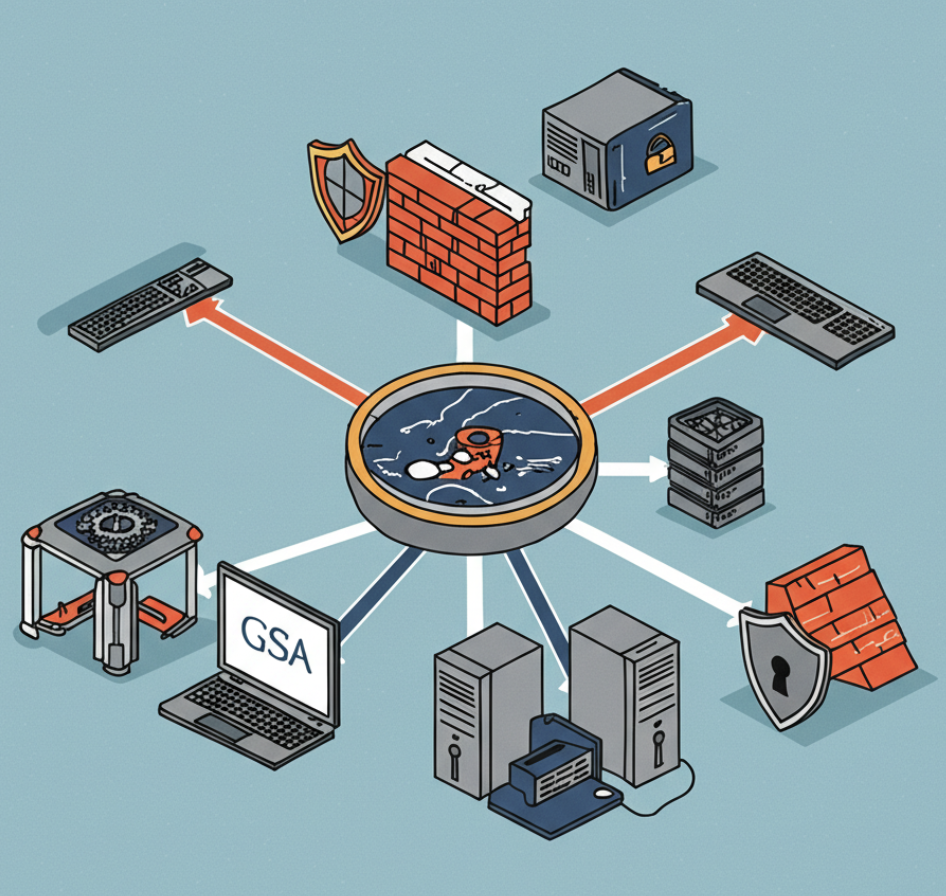
This isn’t just another federal initiative—it’s a full-scale operation designed to enhance the nation’s cybersecurity resilience. At the heart of this transformation is FedRAMP (Federal Risk and Authorization Management Program), the federal government’s trusted system for assessing, authorizing, and monitoring cloud service providers.
But as more agencies shift to the cloud, the reporting requirements have grown more complex, demanding a more agile, precise, and transparent approach. That’s where the OMB-GSA alliance kicks into overdrive. With FedRAMP modernization, they’re cutting red tape, speeding up approvals, and putting actionable data into the hands of the cyber warriors on the front lines.
Inside the OMB-GSA Cyber Partnership
Let’s break it down:
- OMB brings the strategic oversight. It’s the nerve center of executive-level budget and policy coordination.
- GSA brings the operational muscle, managing tech procurement and securing cloud vendors.
Together, they’re combining policy and execution to create a seamless cybersecurity ecosystem across federal agencies.
Think of it as your perfect tag team: OMB sets the mission parameters, and GSA executes with precision. The result? Faster authorization times, smarter data pipelines, and more cyber-secure cloud deployments than ever before.
Real-Time Metrics. Total Visibility. Mission Accomplished.
One of the most critical upgrades from this collaboration is the development of real-time cybersecurity metrics. These metrics aren’t just numbers—they’re mission-critical data points that let agencies monitor their security posture minute by minute.
With machine learning and advanced analytics, the system now aggregates and anonymizes cybersecurity performance data across the entire federal landscape. The outcome?
- A 360-degree view of where we stand.
- Pinpoint accuracy in identifying vulnerabilities.
- More informed decisions at every level of command.
This level of visibility empowers cybersecurity professionals to prioritize what matters most—securing our nation’s data assets with confidence, clarity, and speed.
Cutting Through Bureaucracy—Accelerating Cyber Outcomes
Here’s the deal: the OMB-GSA partnership isn’t about process. It’s about performance. They’ve eliminated unnecessary bottlenecks and reduced the compliance burden on agencies. That means cybersecurity teams can spend less time on paperwork and more time stopping breaches, reinforcing systems, and executing strategic initiatives.
This isn’t theory. This is action. This is federal cyber transformation in motion.
What It Means for Cybersecurity Professionals
If you’re in the trenches—whether you’re a CISO, an analyst, or a risk officer—this is your signal flare. The tools are getting sharper. The data is getting cleaner. The mission objectives are clearer than ever before. The OMB-GSA collaboration is arming federal cybersecurity professionals with everything they need to:
- Accelerate cloud adoption with confidence
- Make faster, smarter investment decisions
- Build resilient, threat-ready infrastructures
- Deliver results that protect systems and serve the American people
Leading with Intent. Delivering with Precision.
This isn’t just a win for interagency cooperation—it’s a new blueprint for operational excellence. It proves what’s possible when agencies stop working in silos and start flying in formation.
The FedRAMP modernization mission is about setting a new bar for what cybersecurity can and should look like in government. It’s about making excellence the default. It’s about moving with purpose, acting with speed, and staying laser-focused on the ultimate goal: securing America’s digital future.
Conclusion: The Cyber Mission Continues
This isn’t a story about compliance—it’s a mission about courage, coordination, and clarity of vision. The OMB and GSA have demonstrated what true leadership looks like in a digital age where threats are relentless and the stakes couldn’t be higher.
So to every federal cybersecurity pro out there: the tools are ready, the systems are aligned, and the mission is clear. It’s time to engage.





