Adaptive Risk Scoring Based on Dynamic Attack Graphs and Threat Intelligence Fusion
As the threat landscape continues to evolve, organizations are facing an unprecedented level of cyber attacks. Traditional risk scoring methods are no longer effective in keeping pace with the sophistication and complexity of modern cyber threats. This is where adaptive risk scoring based on dynamic attack graphs and threat intelligence fusion comes into play. By integrating threat intelligence into risk scoring, organizations can proactively identify and respond to potential threats, thereby reducing the attack surface.
In this article, we will delve into the concept of adaptive risk scoring, dynamic attack graphs, and threat intelligence fusion. We will explore the benefits and challenges of implementing this approach and provide insights into how organizations can leverage these technologies to enhance their cybersecurity posture.

Dynamic Attack Graphs: A Game-Changer in Cybersecurity
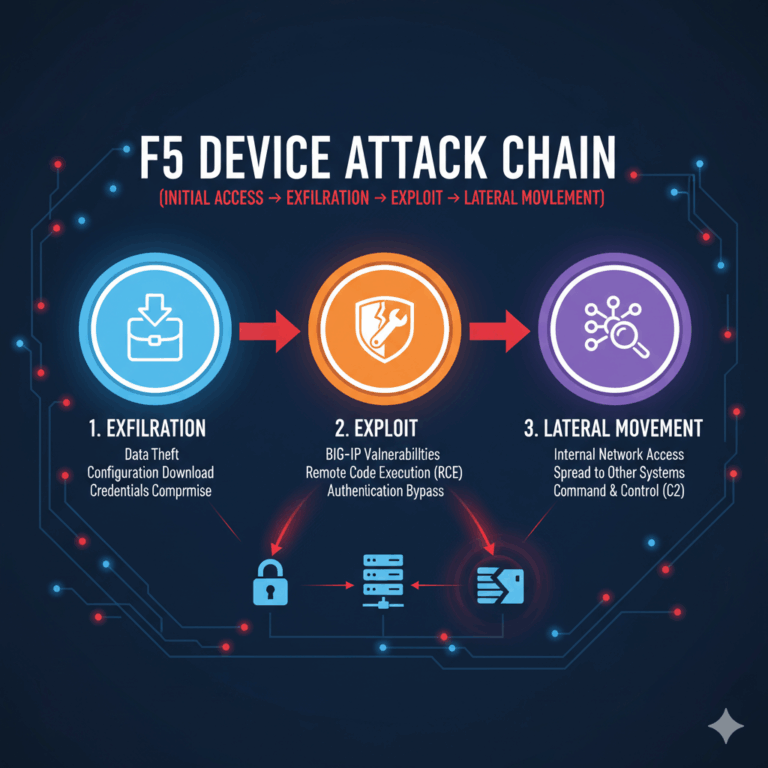
Dynamic attack graphs are a visual representation of potential attack paths that an attacker can take to compromise a network. They provide a comprehensive view of the attack surface, enabling organizations to identify vulnerabilities and prioritize remediation efforts. Unlike traditional risk assessment methods, dynamic attack graphs are constantly updated to reflect changes in the threat landscape, making them an essential tool in adaptive risk scoring.
By analyzing network traffic, system logs, and other data sources, dynamic attack graphs can identify potential attack vectors, including zero-day exploits, misconfigured systems, and social engineering tactics. This information can be used to develop proactive defense strategies, such as patch management, access control, and incident response planning.
According to a recent study by the National Institute of Standards and Technology (NIST), 90% of all network attacks exploit known vulnerabilities. Dynamic attack graphs can help organizations identify these vulnerabilities and prioritize remediation efforts, thereby reducing the attack surface.
Threat Intelligence Fusion: Enhancing Adaptive Risk Scoring
Threat intelligence fusion refers to the process of collecting, correlating, and analyzing threat data from various sources, including open-source intelligence, commercial threat feeds, and internal security information. This information is then used to identify potential threats and enhance adaptive risk scoring.
Threat intelligence fusion provides valuable insights into attacker tactics, techniques, and procedures (TTPs), enabling organizations to develop targeted defense strategies. By integrating threat intelligence into adaptive risk scoring, organizations can proactively identify and respond to potential threats, reducing the mean time to detect (MTTD) and mean time to respond (MTTR).
For instance, threat intelligence can be used to identify malicious IP addresses, domains, and URLs, which can then be integrated into adaptive risk scoring to identify potential threats. This information can also be used to enhance incident response planning, ensuring that organizations are better equipped to respond to threats in real-time.
Implementing Adaptive Risk Scoring: Challenges and Opportunities
Implementing adaptive risk scoring based on dynamic attack graphs and threat intelligence fusion presents several challenges, including data integration, scalability, and analytics complexity. However, the benefits of this approach far outweigh the challenges.
One of the primary challenges is integrating threat intelligence data from various sources, including open-source intelligence, commercial threat feeds, and internal security information. This requires advanced analytics capabilities, including machine learning and natural language processing.
Another challenge is scalability. As the threat landscape continues to evolve, organizations need to ensure that their adaptive risk scoring systems can scale to meet the demands of increased threat data.
Despite these challenges, adaptive risk scoring presents several opportunities, including enhanced threat detection, reduced false positives, and improved incident response. By integrating threat intelligence into adaptive risk scoring, organizations can proactively identify and respond to potential threats, reducing the attack surface and enhancing their overall cybersecurity posture.
Conclusion
In conclusion, adaptive risk scoring based on dynamic attack graphs and threat intelligence fusion is a game-changer in cybersecurity. By integrating threat intelligence into risk scoring, organizations can proactively identify and respond to potential threats, reducing the attack surface and enhancing their overall cybersecurity posture. While implementing this approach presents several challenges, the benefits far outweigh the costs. As the threat landscape continues to evolve, organizations must adapt their risk scoring methods to keep pace with the sophistication and complexity of modern cyber threats.
References Cited:
1. National Institute of Standards and Technology (NIST)