Internet of Things IoT
The Explosion of IoT and Its Impact on Industries
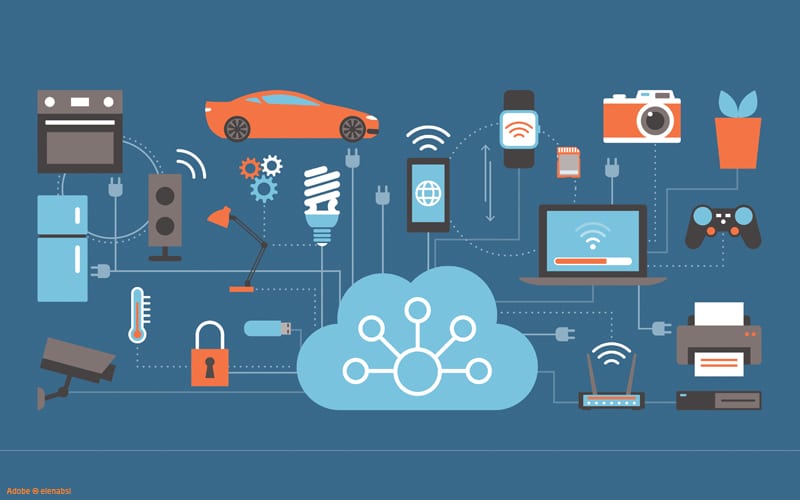
The world is being rewritten in code, and at the heart of this digital renaissance is the Internet of Things (IoT). Billions of devices—sensors, cameras, wearables, industrial machines—are now interconnected, creating an ecosystem that promises efficiency, automation, and intelligence at a scale never before imagined. By 2030, experts predict there will be over 29 billion IoT devices globally (Statista, 2023).
From smart cities that optimize energy use to healthcare systems that monitor patient vitals in real time, IoT is revolutionizing every industry. In manufacturing, predictive maintenance saves billions by preventing unplanned downtime. In agriculture, connected sensors optimize water usage and increase crop yields. Retailers harness IoT-driven analytics to create personalized customer experiences. But with all this innovation comes a fundamental problem—security.
Security Vulnerabilities Baked into IoT’s DNA
Here’s the harsh reality: IoT was built for connectivity, not security. These devices are often designed with cost and convenience as the primary considerations, leaving security as an afterthought. Weak default passwords, unpatched firmware, and unsecured communication protocols make them low-hanging fruit for cybercriminals.
Consider the Mirai botnet attack of 2016, where unsecured IoT devices were hijacked to launch one of the largest DDoS attacks in history (Antonakakis et al., 2017). That was just the beginning. Today, threat actors exploit IoT weaknesses to infiltrate corporate networks, compromise critical infrastructure, and steal sensitive data.
Why the Current Security Model is Broken
The cybersecurity industry has been playing catch-up, applying outdated IT security principles to an IoT world that operates under entirely different rules. Traditional perimeter-based security—firewalls, VPNs, endpoint protection—fails in an environment where devices are mobile, diverse, and often unpatchable.
Most IoT devices have a lifecycle spanning decades, but security updates, if they exist, are often neglected. Worse, many enterprises don’t even have visibility into all their IoT assets, making it impossible to secure what they can’t see. This fragmented security approach has led to an exponential rise in IoT breaches, with attacks targeting IoT devices increasing by 400% in the last two years alone (IoT World, 2023).
The Need for a New Security Paradigm
The old ways won’t cut it. We need a radical rethink—a security paradigm designed from the ground up for IoT’s unique challenges. The answer lies in:
- Zero Trust Architecture (ZTA): Assume every device is compromised until proven otherwise. Continuous authentication and least-privilege access must become the standard.
- AI-driven Threat Detection: Automation is key. AI-powered anomaly detection can help identify malicious activities in real time.
- End-to-End Encryption: Every data transmission must be secured. No more plain-text communications.
- Device Identity and Trust Management: Strong authentication mechanisms, such as hardware-based roots of trust, are essential.
- Regulatory and Industry Standards: Governments and enterprises must enforce stricter security requirements on IoT manufacturers.
The IoT revolution isn’t slowing down, but neither are the threats. The choice is clear: either we reimagine security from first principles or we let the vulnerabilities of IoT become our downfall.
In Part 2, we’ll dive into an even greater cybersecurity threat—the convergence of IT and Operational Technology (OT). It’s a disaster waiting to happen, and unless we act now, the consequences could be catastrophic.
References
- Antonakakis, M., et al. (2017). “Understanding the Mirai Botnet.” Proceedings of USENIX Security Symposium.
- Statista. (2023). “Number of IoT Connected Devices Worldwide 2010-2030.”
- IoT World Today. (2023). “IoT Malware Attacks Jump 400% .”







