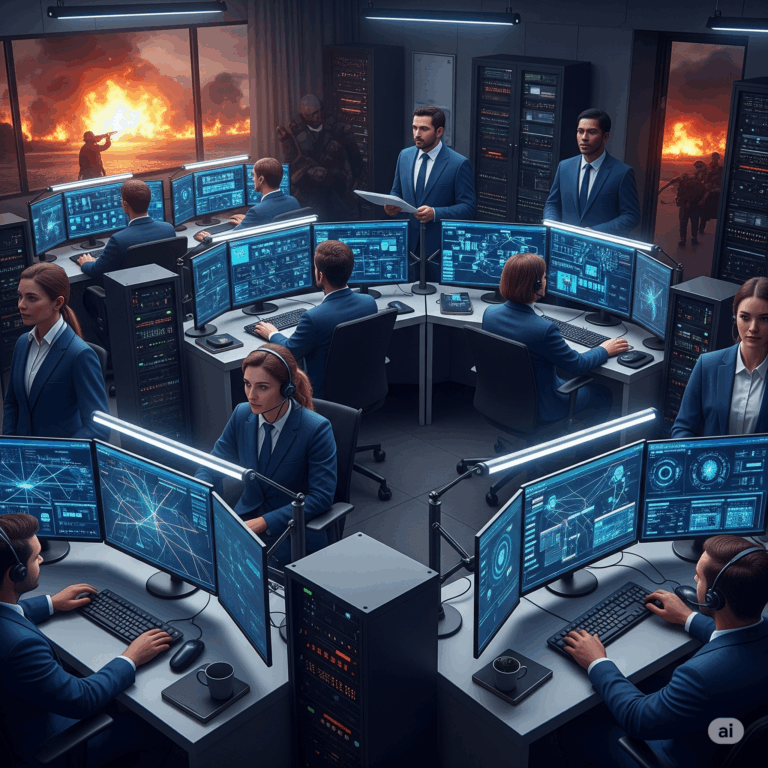
As artificial intelligence (AI), automation, and machine learning become increasingly integrated into IT systems, many professionals wonder: Are humans still necessary to manage these systems? Despite the advancements, the answer is a resounding yes. Human oversight remains critical for operational success, security, and strategic direction in today’s complex IT environments.
The Human Role in an AI-Driven Ecosystem
AI technologies are accelerating incident response, reducing manual workloads, and analyzing massive datasets in real time. However, these systems still require human input to operate effectively.
Contextual Understanding Cannot Be Automated
AI lacks the deep contextual awareness that experienced professionals bring to IT management. While automation can execute tasks, it doesn’t comprehend business context, policy nuance, or ethical implications. For example, when AI flags a security anomaly, it may not distinguish between an actual threat and an expected deviation during a scheduled update.
Strategic Oversight Is Uniquely Human
Humans make decisions based on organizational goals, long-term strategy, and risk appetite. While AI can optimize for speed or efficiency, it doesn’t understand trade-offs that align with broader business objectives. Leadership decisions in cybersecurity and IT governance still require judgment, diplomacy, and stakeholder alignment.
The Limits of AI in Real-World Scenarios
Despite its power, AI isn’t perfect. It struggles in dynamic, ambiguous, or evolving environments where incomplete data is the norm.
Bias and Error in AI Systems
AI systems are only as good as the data and models behind them. Poor data hygiene, outdated training sets, or misconfigured algorithms can produce inaccurate or even dangerous results. Human operators are essential for validating outputs and correcting course when necessary.
Unforeseen Edge Cases
AI can falter when confronted with novel situations. For example, a zero-day exploit or an emerging ransomware variant may escape detection by existing AI tools. Cybersecurity professionals must apply intuition, experience, and creative thinking—capabilities machines simply don’t possess.
Maintaining Trust and Accountability
One of the most important reasons humans must remain in control is accountability.
Legal and Ethical Responsibility
When an automated system fails—whether it’s an outage or a data breach—humans are held responsible. Organizations can’t outsource liability to an algorithm. Compliance frameworks like NIST, FedRAMP, and CMMC also mandate human oversight and auditability to maintain trust and certification status.
Transparency and Interpretability
AI decisions can be difficult to interpret, especially with complex neural networks. IT leaders and compliance officers must understand how decisions are made to ensure they’re defensible to regulators, customers, and partners. Human expertise bridges the gap between machine output and real-world understanding.
Collaboration, Not Competition
Rather than replacing humans, AI and automation should augment them.
Augmenting Human Capabilities
AI can streamline repetitive tasks such as log correlation, threat scoring, or system patching. This frees IT professionals to focus on higher-value work like architecture design, incident analysis, and strategic planning.
Building Smarter Teams
The future of IT is hybrid—teams that combine the precision and scale of AI with the flexibility and judgment of skilled professionals. Upskilling workers to understand and manage AI tools will be just as important as the tools themselves.
Human-Centered Design for Secure IT
IT systems must be built around human workflows—not the other way around.
Resilience Through Redundancy
Human operators provide a fail-safe layer in case automated systems break down or behave unpredictably. This redundancy is critical in government and critical infrastructure environments where uptime and integrity are non-negotiable.
User-Centric Operations
From change management to user access control, people are often the weakest—and strongest—link in IT systems. Training, culture, and communication are key components that no algorithm can enforce on its own.
What’s Next in This Series?
In the next article, we’ll dive deeper into how AI can be integrated into cybersecurity operations without compromising governance or security protocols. We’ll explore architecture models, best practices, and compliance concerns that every IT leader should understand.
References Cited:
1 NIST: Artificial Intelligence Risk Management Framework (AI RMF)
2 Harvard Business Review – Why AI Needs Human Oversight
3 Gartner: Top Strategic Technology Trends
4 CISA: Role of Human Intelligence in Cybersecurity