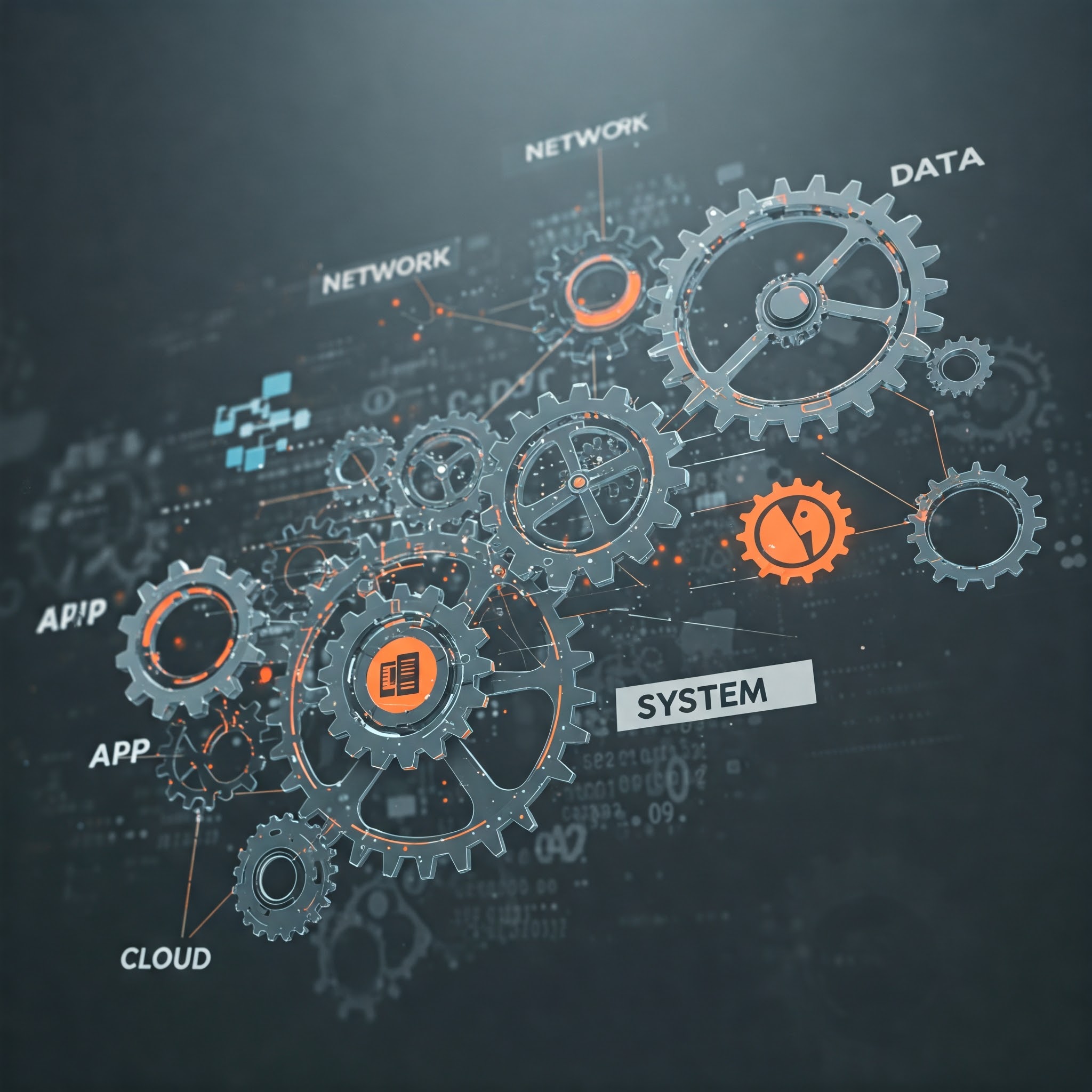
Building upon the essential concepts discussed in Mastering Foundational Security Principles for InfoSec Professionals, we now transition to the practical application of cybersecurity knowledge. Understanding the foundational principles is vital, yet securing modern digital environments demands hands-on expertise across several core technical security domains. These domains represent the specific areas where professionals implement controls, configure defenses, and actively protect organizational assets from threats. Mastering these skills is fundamental to an effective cybersecurity posture.
Information security professionals must possess practical capabilities to safeguard diverse technological landscapes. Subsequently, they need proficiency in areas ranging from network infrastructure to the applications running upon it. Let’s explore these critical technical areas.
Network Security: Defending the Perimeter and Beyond
Securing the network remains a primary focus, as it often serves as the first line of defense and the conduit for internal communication. Effective network security involves implementing multiple layers of controls. Professionals must therefore understand and manage:
- Firewalls: Configuring rules to control incoming and outgoing network traffic based on predetermined security policies.
- Intrusion Detection/Prevention Systems (IDS/IPS): Deploying systems to monitor network traffic for malicious activity and block threats automatically.
- VPNs and Secure Remote Access: Establishing encrypted connections for remote users and site-to-site links.
- Network Segmentation: Dividing the network into smaller, isolated zones to limit the impact of a potential breach.
- Wireless Security: Implementing robust protocols like WPA3 and authentication mechanisms (e.g., EAP) to secure wireless networks**1**.
System Security: Hardening the Endpoints
Every device connected to the network, from servers to laptops, presents a potential attack vector. Consequently, robust system security practices are essential. This involves securing the operating systems and applications running on these endpoints. Key activities include:
- Operating System (OS) Hardening: Applying secure configuration baselines, such as those provided by CIS Benchmarks**2**, to minimize the attack surface.
- Endpoint Protection (EPP/EDR): Deploying advanced antivirus, anti-malware, and endpoint detection and response solutions.
- Patch Management: Regularly applying security updates to operating systems and applications to fix known vulnerabilities.
- Virtualization Security: Implementing specific controls to secure virtual machines, containers, and hypervisors.
Application Security: Protecting Software Assets
Applications, particularly web applications, are frequent targets for attackers seeking access to sensitive data. Application security focuses on finding, fixing, and preventing vulnerabilities within software. This is a critical core technical security domain requiring specialized knowledge:
- Secure Coding Practices: Understanding and implementing secure development techniques to avoid common flaws like those listed in the OWASP Top 10**3**.
- Vulnerability Scanning (SAST/DAST): Utilizing tools to analyze source code (Static Application Security Testing) and running applications (Dynamic Application Security Testing) for weaknesses.
- Web Application Firewalls (WAFs): Deploying firewalls specifically designed to filter and monitor HTTP traffic to and from a web application.
Cloud Security: Navigating Shared Responsibilities
As organizations increasingly migrate to the cloud, understanding cloud security principles is non-negotiable. Cloud environments introduce unique challenges, including the shared responsibility model where security tasks are divided between the provider and the customer**4**. Essential technical security skills in the cloud involve:
- Platform-Specific Security: Configuring security controls native to major cloud platforms (AWS, Azure, GCP).
- Identity and Access Management (IAM): Managing user identities and permissions within the cloud environment rigorously.
- Data Security in the Cloud: Implementing encryption and access controls for cloud storage and databases.
- Configuration Management: Ensuring secure configurations for cloud services and infrastructure-as-code templates.
Data Security Techniques: Implementing Protection
While broader data protection strategies are crucial, specific technical implementations fall within these core domains. This involves the hands-on application of techniques to safeguard data itself. Key technical methods include:
- Encryption Implementation: Applying strong encryption algorithms for data at rest (on storage) and data in transit (across networks).
- Data Loss Prevention (DLP) Tools: Configuring technical solutions to monitor and prevent sensitive data from leaving organizational control.
Mastering these core technical security domains enables professionals to build and maintain robust defenses. Each domain requires continuous learning and adaptation as technologies and threats evolve. Possessing this practical, hands-on security expertise is crucial for effectively protecting modern IT environments.
What’s Next in This Series?
Having covered foundational principles and core technical skills, the next article shifts focus to the strategic context: [Link to Child Article 3: Navigating Risk Management and Compliance in Cybersecurity]. We will explore how technical efforts align with business objectives and regulatory demands. Also revisit the series introduction What Cybersecurity Knowledge Should Information Security Professionals Know? or explore other key areas like [Link to Child Article 4: Essentials of Security Operations and Incident Response] and [Link to Child Article 5: Implementing Effective Identity, Access, and Data Protection Strategies].
References Cited:
- 1 Cybersecurity & Infrastructure Security Agency (CISA). (n.d.). Securing Wireless Networks. Retrieved April 13, 2025, from [Use a relevant CISA page if available, e.g., related to best practices or specific guidance] Note: Replace bracketed text with actual relevant URL or omit if none found.
- 2 Center for Internet Security (CIS). (n.d.). CIS Benchmarks. Retrieved April 13, 2025, from https://www.cisecurity.org/cis-benchmarks/
- 3 OWASP Foundation. (n.d.). OWASP Top 10. Retrieved April 13, 2025, from https://owasp.org/www-project-top-ten/
- 4 Cloud Security Alliance (CSA). (n.d.). Security Guidance for Critical Areas of Focus in Cloud Computing.