There’s a crossroads every young professional faces, and nowhere is this more true than in the world of cybersecurity. It’s a field defined by complexity, by constant evolution, and by the hard truth that a single mistake can lead to disaster—for individuals and organizations alike.
A recent conversation with Dillon Smith, a cybersecurity student at Utah State University, navigating this very challenge, brought these realities to light. The discussion was full of energy, ideas, and hard-won advice from Eric Adams, a CISO who shared insights about the highs and lows of the industry.

The Challenge of Breaking Into Cybersecurity
Dillon raised the kind of question many students and newcomers are quietly wrestling with: “How do you actually break into cybersecurity?” It’s a classic dilemma. Everyone wants experience, but few are willing to offer it to someone starting out. It’s a frustrating loop, and it leaves many people wondering if their hard work will ever translate into real-world opportunities.
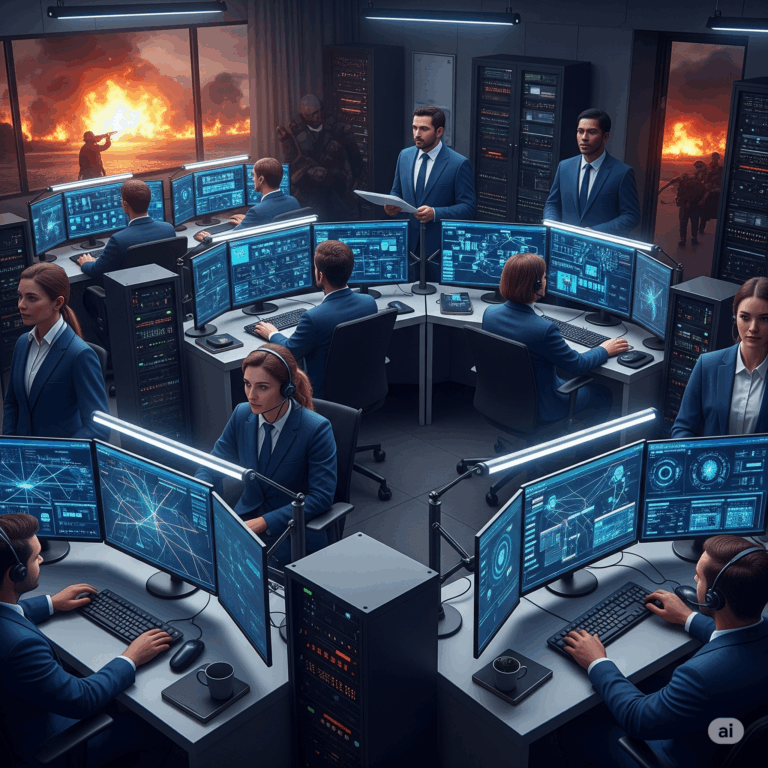
Why the Security Operations Center is a Great Starting Point
One piece of advice stood out: aim for Security Operations Center (SOC) roles. If cybersecurity were a sport, the SOC would be where rookies sharpen their instincts. It’s where you learn the rhythms of attack and defense, where theory meets the messy reality of live systems and human behavior. And if that door isn’t open yet? Look to neighboring roles—help desk, system admin, network support. They’re all valuable. What’s important isn’t the title, it’s how much you’re learning and how much responsibility you’re willing to take on, even when it’s not handed to you on a silver platter.
Why Responsibility is Your Secret Weapon
That, really, was the golden thread through the entire conversation: responsibility. Whether you’re troubleshooting your first ticket or advising an executive on a security strategy, your real job is to lean into the unknown, learn fast, and help others see the bigger picture.
Speaking Business: Translating Tech into Impact
Another standout topic was the importance of bridging the gap between technical knowledge and business thinking. Companies don’t hire security people just because they love firewalls and threat reports. They hire them to protect their ability to operate, serve customers, and stay competitive. If you can translate technical risks into business impact—if you can make it clear why a weak password policy isn’t just a tech problem, but a revenue and reputation risk—you’re already one step ahead of the game.
The Fast Track to Career Growth: Take Initiative
That point was hammered home by a simple truth: people who take initiative tend to rise fast. Whether it’s volunteering for a project, offering help across departments, or taking ownership of a tricky problem no one else wants to touch, the professionals who succeed are the ones who consistently show they can be trusted. It’s not about waiting for permission; it’s about stepping forward, learning the lay of the land, and making yourself useful.
The AI Shift: Adapt or Fall Behind
Dillon also brought up a hot-button topic that every cybersecurity student should be thinking about: artificial intelligence. AI isn’t just changing cybersecurity, it’s changing the nature of work itself. Sure, AI can automate threat detection, flag suspicious emails, and even write code, but it still lacks the full human capacity for judgment. And judgment—understanding the broader context, the trade-offs, the risks and ethics—is where real cybersecurity professionals earn their keep.
AI is a tool, not a replacement. Those who stay curious, flexible, and thoughtful about how AI fits into the bigger picture will find plenty of opportunities. Those who bury their heads in the sand will be left behind.
Standing Out: Becoming a Trusted Go-To Person
Toward the end of the conversation, the focus shifted to career growth. How do you show you’re ready for the next step, even if your current job seems small? The answer: do the basics well, communicate clearly, and put your hand up for stretch projects. Managers notice the people who go beyond their job description, especially the ones who document and share their learning along the way.
Why Cybersecurity is a Team Sport
At its core, cybersecurity is about service. It’s about standing guard over systems and people, confronting both technical and human challenges, and accepting the weight of that responsibility. It’s not easy—but it is meaningful.
And it doesn’t happen alone. One of the last points was about collaboration. The stereotype of the lone security expert, toiling away in isolation, is long outdated. Real security happens when people work together, question each other, and push toward a shared goal.
The Path Forward
So for anyone at the beginning of their cybersecurity journey, the path is both clear and demanding: be curious, be reliable, stay sharp, and never stop learning. The world is full of problems looking for someone capable enough to solve them. Be that person.
References Cited:“What Can a College Student Expect In The Cybersecurity Job Market”.FedNinjas Podcast 2024